MANAGEMENT SOFTWARE
cyberaudit
advanced monitoring and reporting
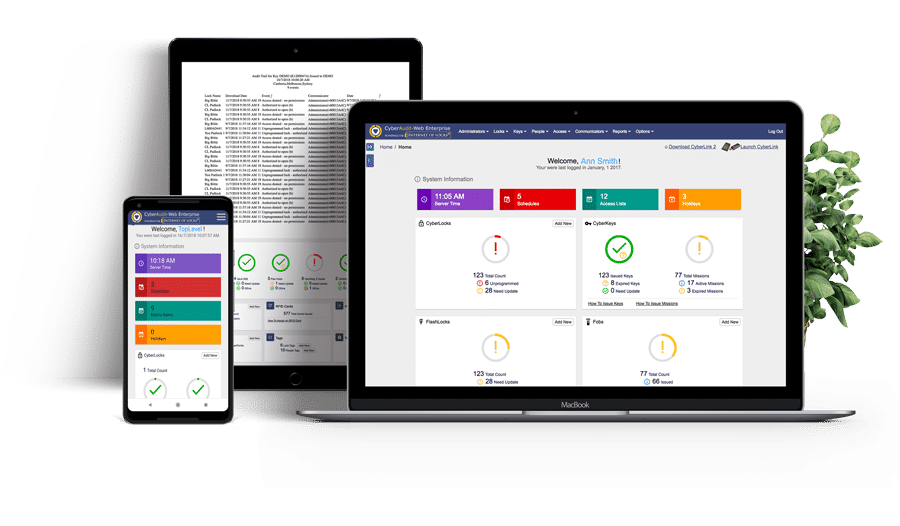
EKA CyberLocks server based software, CyberAudit Web, is designed to simplify the management of your system. The software is available as a self hosted application or a fully supported and managed cloud based solution.
A hierarchy of administrators allows individual managers responsibility for only the CyberLocks and the people in their area. It even manages assets across countries and time zones.
An intuitive point-and-click browser-based interface that uses drop-down information boxes is all that’s needed to access the modules that drive EKA CyberLock’s access control, monitoring and reporting capabilities.
key and custom modules
Location Graphics. Create a graphical interface of your system that allows you to place the location of CyberLocks and Communicators for improved tracking and auditing.
Door & Input / Output Support. Through Flex, manage access to Wiegand-compatible third-party systems such as swipe cards, RFID and biometric readers. Doors can also be set to unlock and relock at certain times and alarms can be triggered if a door is forced or left open.
CyberLocks. See all CyberLocks and individually set access and reporting characteristics. Options include: delayed access, access only with a number of CyberKeys and email notification of denied access.
People and CyberKeys. Allocate individual CyberKeys to users. Set days and times they have access to certain CyberLocks, how soon the CyberKey’s access permissions expire and even revoke a lost CyberKey.
Schedules. Set schedules of who can go where and at what time. This can be as specific as a few minutes at a certain time on one or two days of each week.
Reports. Audit trails can be used to generate tailored reports that tell you who has been where and when. Anything from specific people to user-defined groups such as: contractors, cleaners, security staff and weekend users.
features
- Dashboard reporting with management console
- Over 527 different access events allowing administrators to produce hundreds of different types of reports
- Detailed audit trail
- Set two, three or four-way access
- Denied access email alerts
- Hierarchy of administrators
- Remote key initiation via smart devices
- Key scheduling and expiry
- Set delayed access
- Set group access permissions
- Multiple time zone management
- Monitors and controls third-party systems




